Authored by ‘sundance’ via The Last Refuge,
The Truth Has No Agenda
Everything that preceded the 2020 federal election was a complex system of control by a network of ideologues, federal agencies, allies in the private sector, financial stakeholders and corrupt interests all working toward a common goal.

There’s no need to go through the background of how the election was manipulated and how the government and private sector, specifically social media, worked to influence the 2020 outcome because you have all seen it.
Whether it was local election officials working to control outcomes, federal agencies working to support them (CISA, FBI, DHS), financial interests working to fund them (Zuckerberg et al), or social media platforms controlling the visible content and discussion (Twitter Files, Google, Facebook etc.), the objective was all the same. It was a massive one-sided operation against the freewill of the American voter.
In the aftermath of the 2020 election, those same system operators, govt officials, corporate media, private sector groups and social media platforms then circled the wagons to scatter the evidence of their conduct. If you questioned anything you were a threat. That’s the context to the dynamic that unfolded.
Lawfare operatives joined forces with Democrat staffers, and allies in social media platforms all worked in concert to target the voices of anyone who would rise in opposition to the corruption that was stunningly clear in the outcome of the election process. Corporate media then labeled, isolated, ridiculed and marginalized anyone who dared to point out the obvious.
When AG Merrick Garland says this of January 6, 2021:
[…] “the Justice Department has conducted one of the largest, most complex, and most resource-intensive investigations in our history. We have worked to analyze massive amounts of physical and digital data. We have recovered devices, decrypted electronic messages, triangulated phones, and pored through tens of thousands of hours of video. We have also benefited from tens of thousands of tips we received from the public. Following these digital and physical footprints, we were able to identify hundreds of people.” {link} The targeting operation needs context.
Do you remember on April 27, 2024, when DOJ Inspector General Michael Horowitz said,
“more than 3.4 million search queries into the NSA database took place between Dec. 1st, 2020 and Nov. 30th, 2021, by government officials and/or contractors working on behalf of the federal government.” The result was “more than 1 million searches of private documents and communication of Americans that were illegal and non-compliant,” and over “10,000 federal employees have access to that database.” {OIG Testimony}.
Put the statement from Garland together with the statement from Horowitz, and you get an understanding of what was done.
Hundreds of stakeholders in the Lawfare network joined forces with hundreds of people who became staff researchers for a weaponized Congress. Hundreds more social media background agents then poured thousands of hours into feeding private information to the DOJ, FBI, J6 Committee and all of their hired staff working on the project.
How do I know?…
…I was one of their targets.
Before telling the rest of the story, some background is needed.
I am well versed in the ways of the administrative state and the corrupt systems, institutions and silos that make up our weaponized government. I can (a) see them; (b) predict their activity; and (c) know where their traps and operations are located.
Traveling the deep investigative weeds of the administrative state eventually gives you a set of skills. When people ask how the outlines on this website can seem so far ahead of the sunlight that eventually falls upon the outlined corruption, this is essentially why. When you take these skills on the road, you learn to be a free-range scout, and after a long while you learn how to track the activity.
When I was outlining how the Fourth Branch of Government works and/or Jack’s Magic Coffee Shop and the DHS system operating inside it, I wasn’t shooting from the hip. However, people will always seek to dismiss the uncomfortable truth.
Sometimes you just have to wait for the evidence you know exists to surface, or for a situation to unfold that is driven by a self-fulfilling prophecy. The often uncomfy CTH predictions turn out to be the truth of the issue because they are based on the factual evidence of the issue.
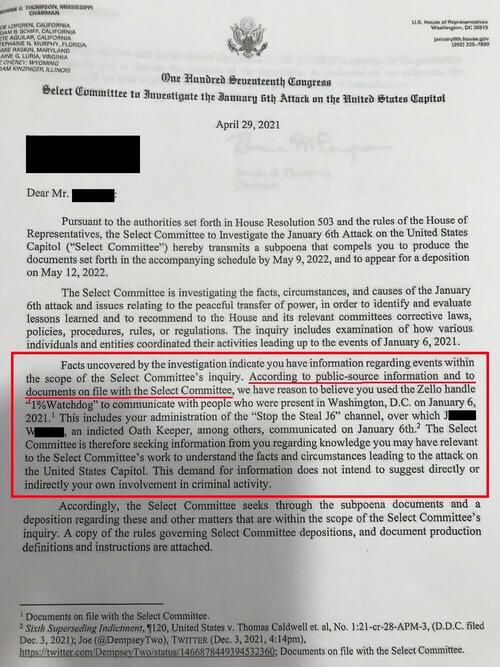
That level of how the system works came in very handy when I received this subpoena from Chairman Bennie Thompson and the J6 Committee. [Warning, things could get uncomfortable if you don’t accept the scale of corruption that exists.]
Pay attention to the red box on the page shown.
This is essentially the probable cause that justifies the subpoena itself.
I have redacted a name in the box for reasons you will see that follow.
I was never in Washington DC on January 6, 2021, nor did I work with or communicate with anyone who was involved in any of the activities that were subject to the J6 committee investigative authority.
I’m going to skip a lot of background noise, irrelevant legal stuff, jurisdictional issues, discoveries from discussions with lawyers and the experience gained in association with this ridiculous subpoena. Instead, I am going to focus on the biggest story within it.
Sticking to the information in the Red Box above, notice how the J6 committee has evidence, “public-source information and documents on file”, showing my participation, communication, and contact with people and technology that are material interests to the committee.
Here’s the kicker…. I had no clue what the hell they were talking about.
There’s not a single aspect of their outline that I had any knowledge or connection of.
I had no idea what Zello was. I had no idea who 1% watchdog might be. I had never heard of “Stop the Steal J6” or associated “channel.” I had never heard of the person redacted, and I had never communicated with any Oath Keeper, any communication system, or platform, or anyone or anything – nothing – that is outlined in that subpoena.
Those points of evidence outlined in the subpoena had no connection to me at all.
The subpoena might as well have been asking me to appear in Michigan because my Red Ferrari was involved in a hit and run accident, during my trip to Detroit.
I don’t own a Ferrari; I have never been to Michigan; I certainly never had an accident; I wasn’t on a trip and have never visited Detroit.
The entire construct of their probable cause for the subpoena was silly. Complete and utter nonsense.
That said, how could there be “public records” and “documentary” evidence of something that never happened?
At first, I thought this was some silly case of mistaken identity and they just sent a subpoena to the wrong person.
However, the investigators were adamant the evidence existed, and the need for testimony was required.
After taking advice from several smart people, and after discovering the costs associated with just the reply to the committee and/or representation therein; suddenly I realized there might be more value for me in this subpoena than the committee. After all, how can there be public-records and documents that I own a red Ferrari and went to Michigan when I don’t and never did.
After several back and forths I discovered, through their admissions of their own research, and through documents they extracted as an outcome of their tasks to prove the merit of their claims, that someone *inside* Twitter had created a fictitious identity of me associated with the networks and communications as the investigators described them.
Think about what was discovered here.
Someone inside the Twitter platform, an employee of Twitter or a person who had the ability to access their administrative system (ie. FBI), had made a decision to target me.
As a result: (a) they had been doing this for a long time with a specific goal in mind; and (b) they created an elaborate trail of background activity and identity that was entirely fabricated.
Eventually, my assigned investigative unit admitted this.
Think about it.
How could they clear me, without them having the underlying evidence that proved my innocence?
Once, the federal investigators realized what took place they wanted to get rid of me -and my snark filled curiosity- with great urgency. They also had an ‘oh shit’ moment, when they contemplated everything, including what they had revealed to me from the outset of my contact, now several months prior.
What I discovered in this experience was that DHS, and by extension DOJ/FBI and the January 6 investigators, had direct administrative level backdoors into all social media platforms.
Overlay the Twitter files now, and then expand your thinking…. Do you remember Elon Musk promising, several times, that he would provide end-to-end encryption on the Twitter Direct Messages? Remember that? It never happened, did it. Why not?
In their quest to prove that I owned a Red Ferrari, traveled to Michigan and had a hit-and-run accident, these investigators outlined to me how the United States Government, through their DHS authority, has employees, agents and contractors with open portals into all social media platforms.
Yes, the federal government is inside the mechanics of the systems (Twitter, Facebook, Meta, Instagram, Google, YouTube, WhatsApp, Zello, etc) and they have administrative access in real time to monitor, review, extract and evaluate everything, soup-to-nuts.
It was only because the investigators and forensic data knuckleheads have these portals, that they were able to locate the source of the fabricated evidence they were originally attributing to me. This was an investigative process and research discovery being conducted in the data processing systems of Twitter in real time as they questioned me.
Once they realized what had taken place, and as soon as I started asking how they were making these admissions (now carrying an apologetic certainty), suddenly the investigators wanted no further contact or communication with me. You’re good, whoopsie daisy, our bad, sorry.
Now, take some time to fully digest and absorb what I have just shared.
The U.S. government is worried about TikTok, because U.S. citizen data might be extracted?
Meanwhile, the U.S. government, at a fully unrestricted administrative level, is inside Twitter, Facebook, Meta, Insta, YouTube etc., running amok and extracting anything – including private messages… and they’re somehow worried about protecting us from TikTok data collection. Think about it.
Maybe the thing that worried them is not that administrators within TikTok were datamining; maybe, just maybe, the thing that really worried them is that they’re not the administrators.
Ears of an elephant, eyes of a mouse.