Data Heist Hotline: Mark Lance’s Quick Dial
Who’s Calling When the Bytes Get Locked?
Mark Lance is the go‑to guy whenever a company’s confidential data gets shackled by cyber shenanigans. When the threat comes through, his phone always rings fast, and he’s on the line before anyone else even knows there’s an emergency.
What the Hackers Are After
- The corp’s data is being held hostage until the ransom drops.
- The attackers keep coming back for that sweet payment.
- The sensitive info is only returned once the money’s in the pocket.
Background Note
This whole saga was first reported by Chris Summers of The Epoch Times, where he laid out the incident with a blend of crisp journalistic style and undeniable human touch.

When a Ransom Note Pops Up, Talk to the Mad‑Hatter First
Mark Lance, the ransomware whisperer at Guidepoint Security, says the real trick in a cyber‑attack isn’t whether you toss cash into a black‑hole, but when you start the conversation. That early dialogue is like pulling a fire alarm to signal the squad, keeping the drama from turning into a full‑blown horror movie.
What Mark Says
- Early is essential: “The earlier we get engaged, the better,” Lance told The Epoch Times.
- Victims usually know they’ve been hit when the ransomware notes appear. It’s like the universe’s way of shaking your hand.
- Even if you’re not sending money, it’s worth talking to the criminals. Why? Because you can buy time—delay the inevitable data dump, giving your forensic team a breather.
- He cites a case where a ransom demand jumped to a staggering $70 million. That’s a lot of zeros to keep quiet.
Why This Matters
Each day in the U.S., corporate giants and state‑run institutions fall prey to ransomware. In the first half of 2025, a Comparitech report found 208 attacks on government agencies worldwide, a 65‑percent jump from the previous year. That’s a lot of “Do you want to keep your files or pay someone else?” moments.
The FBI’s Definition
To keep it simple: Ransomware is a malicious gaggle of software that ties you up, blocks your files or networks, and wants a price tag to unlock them. It’s like a digital villain who whispers, “Move your money, or forever stick to your haystack.”
Bottom Line
The smarter move isn’t just about surviving the threat—you’re looking to preserve your operations, protect the data, and maybe even re‑implement a better security posture afterward. Engage early, negotiate, delay the release, and let your IT heroes finish their job. That’s the game plan that helps most organizations handle ransomware without turning their lives into a financial nightmare.
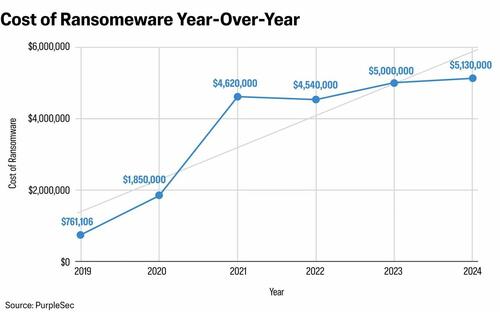
Ransomware’s New Price Tag: From a Six‑Figure Hit to a Half‑Million‑Dollar Disaster
In a seismic shift that would make a high‑end jeweler blush, the average cost to a business that falls victim to a ransomware attack has ballooned from a modest $761,106 in 2019 to a staggering $5.13 million by 2025. According to PurpleSec, a U.S.‑based cybersecurity firm, this figure isn’t just the ransom itself but the whole fallout: recovery effort, support services, and the cascade of hidden costs like reputational damage.
What’s Behind the Numbers?
- Ransom payment – the immediate ask from the bad actors.
- Recovery & restoration – rebuilding systems, restoring data, and hiring specialists.
- Indirect blows – lost revenue, customer churn, legal fines, and the halo of bad press.
When businesses are jolted into a ransomware crisis, they’re often still scrambling to figure out what really happened and what to do next. “They’re not necessarily sure what has fully transpired or has occurred within their environment, to know what they potentially need to do as next steps,” notes Lance, a veteran in cybersecurity with 25 years of experience.
Why the “Environment” Matters
Lance explains that “environment” covers every hardware, software, and network backbone that keeps an organization ticking. In a handful of words: Security is a full system, not just the office door.
Enter the Negotiator: Your Rescue Ranger
When you call in a ransomware negotiator early on, you gain more than a calm voice over the phone. They help you:
- Set realistic expectations about what can be salvaged.
- Offer a realistic “playbook” of next steps.
- Buy you precious time while you consult legal counsel.
- Guide disclosure strategies—whether you need to spill the beans to the public, shareholders, the SEC, or other regulators.
The advantage? If you jump in before the damage festers, the negotiator can pull some critical intel from the attackers—proof of data access and a kind of “file map” (a directory tree) that reveals exactly which files were compromised. “We can gather and glean information from those communications that can be shared, that they might not have otherwise,” Lance says. “But yeah, the earlier [we are brought in], the better.”
Bottom Line: Pay Up, or Pay More
Ransomware is no longer a quick bargain. The new cost reality forces companies to rethink their strategy: unearth the hidden damage, coordinate with lawyers, manage the public narrative, or else let the price tag float. The stakes are high, the numbers are higher, and the moral is simple: Act first, cost later.

Cybersecurity Chaos: From White House Briefings to Ransomware Negotiations
Jeanette Manfra: A White House Warning
On December 19, 2017, Jeanette Manfra, the cyber‑security chief for the Department of Homeland Security, took the stage at the White House and dropped a bombshell: the United States believes that North Korea was the mastermind behind the global WannaCry ransomware attack.
Manfra’s announcement sent ripples across the cyber‑security community. Think of it as the giant every‑man’s drum roll announcing that the enemy is here, and we’re not just talking about a random act of cyber vandalism—we’re dealing with a power‑sized, nation‑level adversary.
Lance: The Riddle of Ransomware Negotiations
In a different corner of the cyber‑warroom, Lance sheds light on how deal‑makers wrestle with ransomware gangs.
- Find the Guest’s Wants: Lance starts by asking the basic question, “What does the client want from the communication with the ransomware gang?”
- Strategic Pacing: Early on, the plan is often just to dilly‑dally—waiting to uncover the attack’s full scope and determine the stakes.
- Negotiation Flip‑Flop: If the victim eventually decides a ransom might be worth it, Lance flips the strategy. Now the focus shifts to how fast the fee is needed, whether the attackers demand prompt payment, or if there is a window for a real back‑and‑forth.
- Client‑Directed Tactics: “Our approach changes with the client’s needs and what they want to pull out of the situation,” Lance explains—essentially tailoring the game plan to each unique piece of the puzzle.
In short: while some folks are shouting “enemy’s at the gate!” from the White House, others are quietly plotting their next move in the shadows of the cyber‑economy, juggling timing, demands, and the ever‑present risk of becoming the next headline.
Cyber Ransom Notes
How Cyber Criminals Drop Their Villainous Vouchers
In most cases, the infamous ransom note isn’t sent via email or text—it slips right onto the desktop of the unlucky victim, as Scott Lance explains.
Once that ominous message pops up, it gives the victim a clear, no‑touch rule: don’t mess with the IT systems. Instead, you’re instructed to:
- Download a Tor browser (because anonymity is key).
- Navigate to a dark‑web site where the attackers are waiting.
- Start talking to them. Think of it as a very shady version of customer support.
In short, the freelancers in the shadows have a pretty simple drop‑in protocol to keep the chaos going.
